|
Introduction
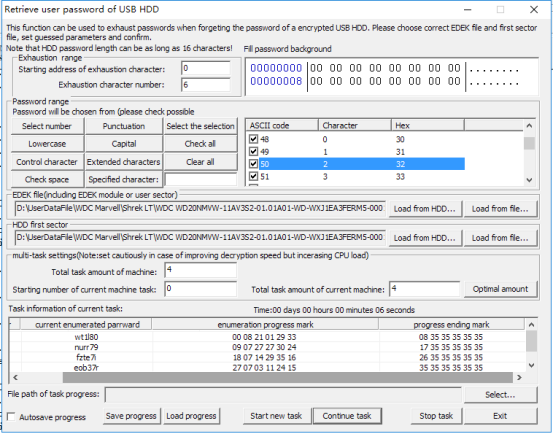
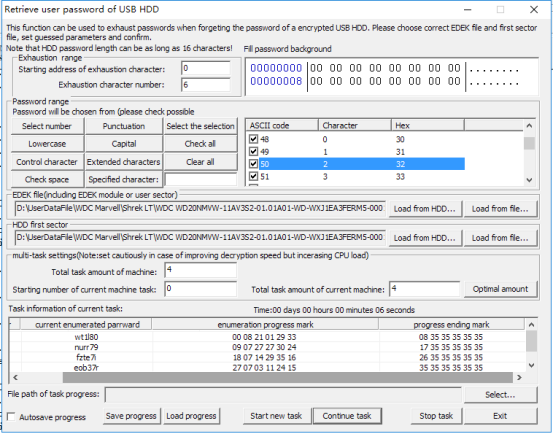
Since WD Mypassport HDDs have a strict encrypting and decrypting system, there is little possibility that data recovery can be performed if the user has forgot the password. In this situation, the function of “Tools -> Retrieve user password of encrypted USB HDD” in WD utility can be used to retrieve the password, which makes it possible to do data recovery.
This function sets guessed parameters based on users’ fuzzy remembrance and the program will automatically guess the users’ password.
Preparation work for using the function:
1. Since the normally-used “HDD first sector” has a specified character “55AA” in the end, the program will consider that the right password has been guessed if this character appears in the encrypted HDD first sector in when decrypting. Therefore, there is an option “Load HDD first sector” when using this function.
2. Meantime, when the HDD is decrypted, “EDEK” data must be obtained. Then a new password will be formed with “EDEK” and “user password”. The new password will be used to decrypt the HDD. Therefore, there is an option “Load EDEK file” when using this function.
3. Both the HDD first sector and EDEK can be obtained from the HDD. However, the first sector we want to obtain is the original data which has not been decrypted. Only in this way, can we get the correct data of the specified character when the program is decrypting. Therefore, the program reads the data from the COM port when it loads data from the HDD. And it requires a good connection of the COM port when we load data from HDD first sector and EDEK. Fortunately, MRT lab has developed a WD USB-to-COM transfer card, “MRT WD-USB”. Anyone who needs it can contact MRT lab.
We can also use the way of changing USB board to SATA board to obtain the data and then save the file. Then when using the function, users can select to load from file. Comparatively, this way is more complex.
Guessed range settings:
1. Explanation of character location: for example, if the password is abcdefg, the address of Character a is 0 and the address of Character d is 3.
2. Guessed range setting rules: for example, if the password if abcdefg.
If we remember the first three characters, but don’t remember the characters behind, then we need to fill “abc” in “Fill password background characters with (hex)” and fill “3” in “Starting address of exhaustion character” and fill “4” in “Exhaustion character number”.
If we forget abc but remember defg, then we need to make the first three characters blank and fill “defg” in “Fill password background characters with (hex)” and fill “0” in “Starting address of exhaustion character” and fill “3” in “Exhaustion character number”.
3. What we have mentioned above is the starting address and length of the guessed password, and the filling requirements of the guessed character. Next we are going to set the characters that may appear in the guessed password. In the panel list, all the alphabets, numbers and specific characters are included and selected by default. If the guessed password only includes numbers or minuscules, then other characters can be cleared and we just need to select numbers or minuscules. If some specified characters are remembered, they can be filled in “specified character” and separated with coma, such as “1,2,a,b”; then click to select “specified character” to make these characters selected in the list.
Multi-machine and multi-task settings:
If only one machine is needed and no special requirements, choose settings by default.
For the task amount of current machine, it is better to use the default number which is set according to the CPU core number. If the number is less than the default number, it will decrease the efficiency. And if the number is more than the default number, it will bring little benefits, either. However, if we don’t want this function to occupy so much CPU resources, we can decrease the number. If there is just one machine, then the number needs to be consistent with the actual number.
When we need to retrieve the password with more than one machine simultaneously, we can refer to the way below:
If we need eight tasks and two machines to work at the same time, the “Total task amount of machine” should be filled with “8” for both of the two machines. At this time, if both the two machines are assigned with four tasks, “Stating number of current machine task” should be filled with “0” for the first machine and “4” for the second machine.
If the “Total task amount of current machine” is “2” for the first machine, the “Stating number of current machine task” should be filled with “2” and the “Total task amount of current machine” for the second machine should be “6”.
Rules: when the task of more than one machine is being set, “Total task amount of machine” should be consistent for every machine. “Stating number of current machine task” of the machine behind is the sum of the total task amount of all the machines.
|